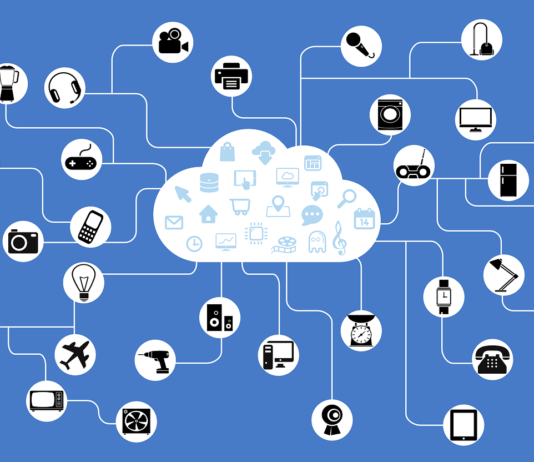
What Are the Most Common IoT Security Threats in Today’s World?
It doesn’t take more than a few seconds for your email composed in Bahrain to reach the outskirts of central United States. Clothing purchased...
Learn the Design Principles that are used on Connected Devices
The aesthetic design of a connected device is not of concern in an IoT project. The design aspects of concern are the interaction with...
6 Easy Ways to Access Blocked Websites
The instances of websites being blocked are on the rise each year due to various factors. In many countries, increased censorship has led governments...
How Will Artificial Intelligence Impact IoT in 2018
ogWe have come so far since the early days of an Internet of things (IoT) and artificial intelligence when things seemed new. Here is...
Is Learning IoT Worth Your Time & Investment?
Every person who has even the slightest hint of what's going on in the technological world would be aware, or at least have heard...
2 Favorite Strains You Can Grow On The Balcony By Tia Moskalenko From AskGrowers
Are you looking to grow your favorite cannabis strain on your balcony? Here are top suggestions from AskGrowers experts that will give you impressive...
What Is Diffie Hellman Key Exchange?
The key exchange problem is an important and well-studied problem in the area of cryptography and information security. The problem is regarding how two...
10 Ways The Healthcare Industry Is Using Online Learning
The landscape of healthcare and medical education is rapidly evolving for the better, thanks to the integration of online learning into numerous aspects of...
Tone In Writing – Why It Matters, How To Improve
Words have an impact that extends well beyond their literal meaning. The tone, or the attitude and emotion conveyed by your word choices, pivotally...
Driving Innovation In Enterprises Through Bimodal IT
We live in an age of digital transformation. The success of any enterprise today depends heavily on how well it can transform and distribute...