
There used to be a time when life on the internet was a lot simpler. Let’s say that you had an account that you wanted to keep protected, you only had to use a log-in id and a password. But that was before the hacking community got smart! With time, the one-step passwords have turned out to be extremely vulnerable to the insistent overtures of diligent hackers. The time had come for a one-stop security fix to emerge and the two step authentication process came up with the juat the thing one would need.
Right from the time of its inception, the two factor authentication (more commonly known as 2FA) has made its significance quite clear. Since 2012, several consumer tech companies and individual users have adopted the concept of 2FA as a bible to cybersecurity. Back in the day, the two factor authentication process had made quite the reputation for being a simple yet effective way to keep account takeovers at bay.
What happened 5 years down the line? Today, we live in a cyber world where almost all major web services provide the 2FA in some form, to varying degrees. This, instead of keeping hackers away, seemed to court their attention even more as the seasoned ones found out exhilarating ways to bypass the weaker implementations.
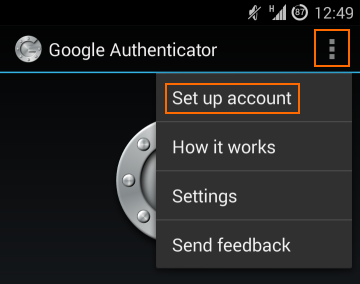
Now, the chances are if you have heard anything about the two factor authentication process, then you already know about the Google Authenticator, a convenient little app. available for Android and IOS. The question is, why should you use it?
Read on to know more about how Google Authenticator will add a formidable layer of defence against account theft.
Less complex for the user- Here’s the thing about two factor authentication process. Though it steps up cybersecurity, sometimes it can get difficult to navigate. Initially, the complexity of this two level security process (as compared to a single password) kept it from being an instant favourite with the users. With time though as people realised what it has to offer, many went on to acknowledge the necessity of the 2FA.
What makes Google Authentication stand out is its easy-to-use user interface. This app is compatible with a large range of devices, including the old versions of Android (Android 2.2 and above). The size of this application is less than 2MB, thus functioning smoothly on devices with less RAM and storage.
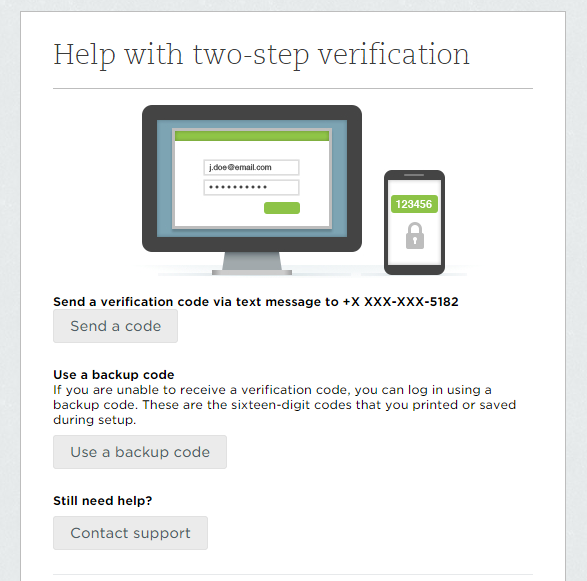
Every 60 seconds, a new code- To better comprehend the functioning of two factor authentication, it is first necessary to understand that not every one of them were created the same way. While some varieties ensure solid security, the others should be avoided downright. One of the methods of verification uses SMS text to send you a code. It is said to be the most hack-prone zone. The backup codes can compromise your security to an intruder much as a bad app on your device, one that has the permission to access your SMS.
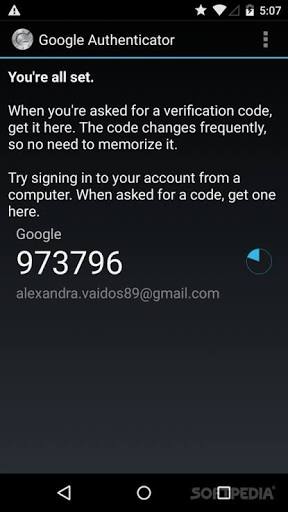
Here is how Google Authentication does things differently. This app works independently to ensure that no other app can view these codes and no other person can misuse them (as long as your device is safe and secure). Also, Google Authenticate works based on a TOTP algorithm, courtesy of which it generates a new code every 60 seconds thus making it a much more secure and convenient option for 2-step verification. Sounds formidable to you? Well, it does to the hackers!
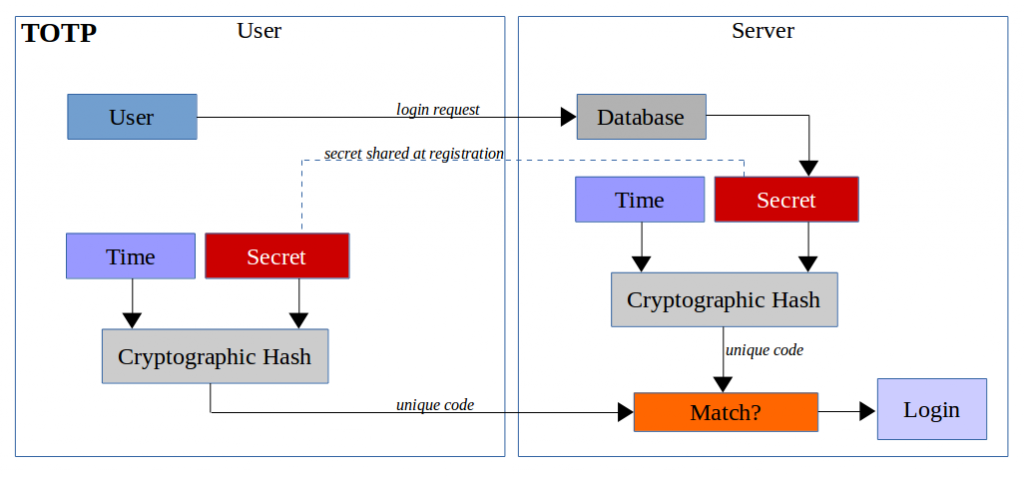
Time-based OTP algorithm- Speaking of, the Time based One-Time Password (TOTP) algorithm is one that generates an OTP by combining a shared secret key and the current time using a cryptographic hash function. With TOPT, the same code is generated on your device as well as on the Google site, thereby providing you with access as the codes match.
The TOPT algorithm enables Google Authenticator to function offline without requiring any sort of internet connectivity on your device. This is what makes Google Authenticator the most formidable thing to enhance your account security because unlike with other 2FAs, you don’t have to worry about being burnt out just because you are outside the coverage area.
Simplifies the task of managing multiple accounts – Here’s a scenario that we would like you to imagine. Let’s say that you have multiple Google accounts, one for work, one for personal use and one for any other reason. Let us say that all these accounts are equally invaluable to you and you want to enable two factor authentication for all of them. Now, you already know that you cannot use the same phone number for multiple accounts. So, try picturing yourself jostling to manage your accounts effectively, knowing that you will get a code in different number for different accounts every time you try to use them.
Google Authenticator cuts through all these hassles and makes it look like a cakewalk. With this app in your smartphone you will now have the codes for all your accounts safely at one place. All you have to do is set-up each account with this app, and that should get you done.

Not restricted to Google accounts only – Do not let the name confuse you. Google Authenticator, as the name might suggest, is not restricted to Google accounts only. This means now you have a formidable layer of protection around other popular sites like Facebook, Twitter, Outlook, Dropbox, Evernote etc. The set-up process for these sites are similar to what you did with your Google account. You just have to scan the QR code and there you go! Your accounts are now thoroughly protected from the clutches of sneaky hackers.
As a two factor authentication service, it remains to be said that Google Authentication app performs brilliantly and outshines many of its contemporaries simple due to smart coding, interesting algorithm and ease of access. It truly embodies the one stop security solution that the 2FA was supposed to represent. It is safe and easy to use and does its job extremely well at keeping away the mischief mongers of the cyberspace. If that does not sound like a formidable layer of protection, then what does?


