Like everything in existence, crimes too go through a process of evolution. The need of some people to cause misery to others in order to quench their personal sadistic nature has now taken a digital revolution. In the past, excruciating wars would drag people from both sides to their crimson ends. Now, the risk of mutual annihilation is reduced, with the emergence of a technology that spans across almost all nations- the internet.
Verbal spats to bully people is a huge “hit“ these days on social media. Just pick a controversial topic and share your opinion on any digital platform. Hate speech against racial minorities, LGBT, political figures, has become commonplace. This is termed as cyber-bullying which is just the most feeble of actions in the hierarchy of cyber-abuse. Social media has also been used for recruiting people for groups like ISIS and other neo-nazi groups. So, you can imagine if your personal social media is not safe from such terrors, what would be the safety situation of other platforms?
We are living in the most technologically progressive time and though things are not as chaotic as before (You know, famine, war, plagues), it is still not completely safe to go about your daily routine. Especially, if you are an ardent user of the internet. So, let us glance over some of the possible cybersecurity threats that might emanate out in 2019.
#1. Sophisticated Phishing
People now have a decent idea about which information to share and which are strictly not to be disclosed such as OTPs or ATM passwords on phones as well as on emails. But strategies have also evolved for gaining personal information.
Machine learning can be used by such people to create convincing messages to let out their personal information, mainly of a financial nature. Such attacks allow black-hat hackers to get a hold of the user’s login ID, credit card information and even the social security number to wreak havoc on their lives.
#2. State-Sponsored Attacks

While there are numerous nations that are sponsoring actual wars in other states such as Saudi and Iran in Yemen fighting for its control, most take a less gut-wrenching approach to solving conflicts.
When a scenario of war arises, two things are inevitable; carnage and financial ruin. But we still have people who are sponsored by nations to cause harm to other nations, either as a sign of warning or a direct attack on their security. This is the realm of state-sponsored cyber attacks. There have been numerous incidents of two nations battling it out behind the safe haven of anonymity. Usually, such cases echo the names of some particular contenders such as Russia, China, North Korea, and Iran.
Such attackers often target financial institutions of a nation and it has been consistently on the rise. According to Reuters, since 2007, there have been at least 94 financial cyber crimes. 23 out of these have been linked with state-sponsored cyber crimes with a majority coming from Iran, North Korea, and Russia.
In 2019, these attacks can increase leading to a possibility of heated tensions in many nations. These could be attacks on some of the finest infrastructure of the nation that holds pivotal value in terms of strength and security. Cyberwarfare has already become a highly useful tool to mold many global situations, both in offensive as well as defensive cases.
There are many types of hackers but usually, such acts of chaos are done by black-hat hackers. Breaking into a highly protected area has its perks in the form of personal satisfaction and also when the state sponsors you, financial benefits might be high.
To defend themselves, governments and even privately owned institutions use the services of an ethical hacker. Such individuals help in making the system more efficient and secure. Ethical hackers usually have a higher chance of getting jobs. This is because most organizations facing the threats of such attacks on their systems, want to make sure that their systems are safe.
So, if you are devoid of cruel intentions and want to help governments and other institutions, protect themselves from attacks, you can be an ethical hacker as well. Numerous resources exist to learn ethical hacking such as YouTube clips, e-books, and online tutorials. One such online tutorial is the “Ethical Hacking Ultimate Course” which comes with 8 hours of video and covers 14 vital sections. This course is an excellent recommendation for those who are still a novice at the subject and want to gain complete insights into it.
#3. Online Kidnappings and Ransomware

No! You’ll not be physically be sucked into a portal on the abyss of the dark web, but your identity can is always susceptible to hacking.
Such incidents always cost billionaires, millions of dollars. But that is the difference between the physical and the digital world. A person physically kidnapped once returned is usually safe. That cannot be said about the information that is “returned” to the user. Unlike physical reality, in the digital world, you can always make duplicate copies of the data.
With such ransomware going high, companies are building better defenses to safeguard the privacy of their customers. Despite that, high-net-individuals are always in the risk of being targeted.
Also, the rise of crypto-currencies such as Bitcoin is being credited with the increasing attacks of ransomware.
#4. Driverless Cars
While driverless cars are seldom in sight, they are believed to be a huge success in the future. It is said that as much as 90% of cars would be connected to the internet by 2020. Here, with the constant flow of information between these machines and the internet, any hacker with vitriolic intentions can gain access to a heap of personal information.
This is not even the most primary concern. With such access to any vehicle, the hacker can gain complete control of the car and in a sense, over the passenger’s life. But for the majority, that shouldn’t be a threat currently as such vehicles continue to remain exclusive to the top 1% of the population.
Still, the idea is terrifying. While for hackers, it is just another opportunity to find more technological to be exploited.
#5. IoT Attacks
During the dawn of the 1910s when telephones first made their presence in the mansions of the English upper class, to say that they found it hard to be habituated would be an understatement. Technological growth took over from those times and now we have a more connected and compact world.
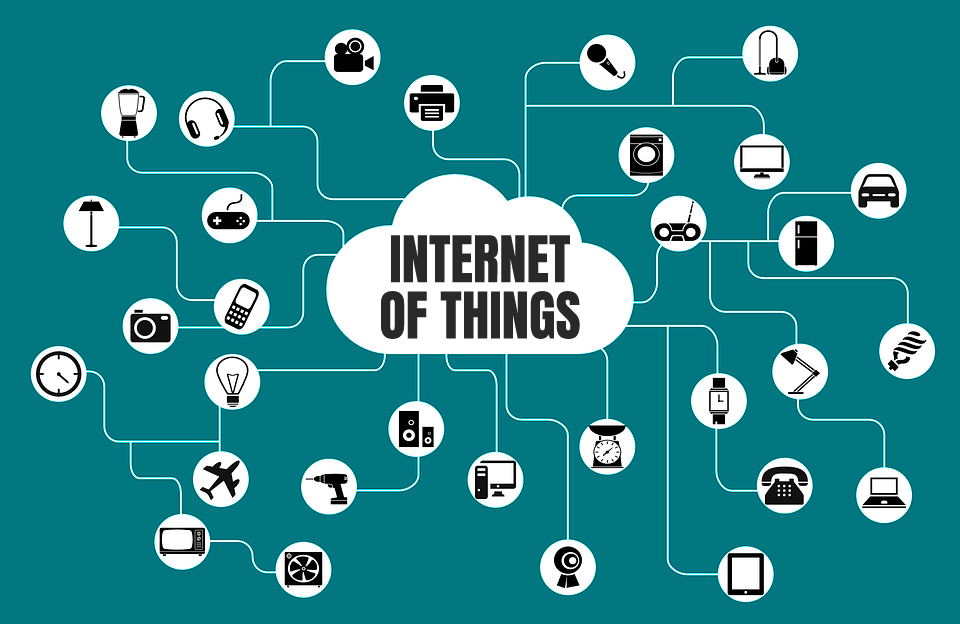
IoT is becoming almost ubiquitous across the world and 2019 will bring a fresh face of IoT with its many trends. As more devices are connected to the internet or with other devices, accessing that information becomes easier for hackers.
The predictions of how bad it can get are left up to one’s imagination but with more devices being part of the IoT, it also increases the risk of vital information being hacked.
Final Thoughts
These are just some of the most possible predictions that will accompany this year. What catalyzes the whole situation is the lack of sufficient people available to defend such attacks i.e. cybersecurity professionals. Companies have not been able to successfully hire strong professionals with in-depth knowledge in this field. This jeopardizes the safety of such companies, opening them up to further attacks.
Predictions currently say that 3.5 million positions would be open for cybersecurity professionals by 2021. However, as of now, without qualified professionals, security systems in organizations continue to be at risk.
But it’s not extremely strenuous to get yourself familiarized with cybersecurity. Online tutorials such as the “CompTIA Cybersecurity Analyst CySA+ (CSA+). The Total Course” that is an excellent tool to know all about the complexities that one has to tackle in cybersecurity. Taught by a highly trained former army intelligence, this course teaches you many of the important things regarding keeping yourself safe from cyber attacks.
If you prefer something meant primarily for the general crowd, you can go for the “Cyber Security For Normal People: Protect Yourself Online” course that comes with 9 sections and 35 lectures. This course is meant mainly for those who want to protect themselves from cyber attacks on their personal devices.



