Understanding Files and Directories Security in Red Hat
Security is no longer used at boundaries and perimeters only, but should be put in your internal network and even inside your systems as well. Each host should defend itself using personal firewalls, Host Intrusion Preventions Systems HIPS, Antivirus software, and etc. Even more, each file and directory should have a mechanism to defend itself too. This is called Defense in Depth.
The concept of user and group ownership of files and directories, together with Permissions set on those files and directories will provide an effective way to secure important system files (like configuration files), and valuable user data. This article is going to tackle this important concept of Manage Files Ownership. So, bring your coffee and give me your attention.
Files and Directories Ownership
Who has the right to enter this house? Certainly, its owner, his family, and whoever people whom the house owner invites (gives permission) to enter his house.
Another question: This document is classified, who has the permission to read it?
A third question: these files contain bank clients’ account balances, which employee and department have the permission to modify these file?
A fourth question: this script (a collection of Linux commands stored in a file, and executed in sequence) performs some system tasks or text processing, who has the right to execute (run) it?
Have you noticed anything in the above four cases?!
– Mmm… yes, three questions out of the four begin with who, and even the different one (beginning with which) asks about person and group of persons.
Yes, exactly!! That is what I mean: When talking about ownership, we are concerned with “who”.
As any object in this life, each file, and each directory should belong to someone: the owner. Ownership in UNIX and Linux dictates that a file or directory is owned by a user and group. I need you to remember this for now; if you get out from this section with this fact only, it will be enough for me.
Permissions
Now, as we know “who” the user and group owners of a file or directory are, it is time to know “what” these owners are allowed to do with the file or directory. So, here we are concerned with what the owners of the file could do.
UNIX and Linux File Security Rules
The following rules describe how access to files and directories is controlled in UNIX and Linux operating systems:
- When a user starts a process, the process runs with effective UID of this user, and with GID of the primary group for this user.
- Each file or directory is owned by a user UID and group GID.
- When a subject (a running process) tries to access an object (a file or directory), the level of access is granted based on the following matrix:
-
Subject UID and Object UID
Subject GID and Object GID
Rules that Apply
Match
Do not care
User’s Permissions Apply
Don’t Match
Match
Group’s Permissions Apply
Don’t Match
Don’t Match
Others’ Permissions Apply.
How Ownership is Determined?
When a new file or directory is created, ownership is determined as follows:
- The user who creates the file becomes its owner.
- The primary group of the user becomes the owner group.
The ownership of a file or directory could be changed only by root. The group ownership of a file or directory could be modified by root and the file owner. While root can change the group to any existing group, a non-root owner could change the group ownership of a file or directory to one of the groups in which he/she is a member.
We will learn how to change the user and group ownership soon.
How Permissions Work?
There are three basic symbols that determine the permissions on a file or directory:
r read.
w write.
x execute
The following table lists the meaning of each symbol in the context of files and directories:
-
Symbol
File’s Context
Directory’s Context
r
Read or copy the file contents.
List directory contents.
w
Edit and modify the file contents.
Create and remove files from the directory.
x
Execute the file as a program.
Change to the directory, and make a long listing of the directory contents.
As we know from the access control matrix discussed above, there are three sets of permissions: user, group, and others. Each set consists of three on/off settings having the following general format:
rwx
The first position denotes the read permission, the second for the write, and the third for the execute. The existence of the letter in its position means the permission is granted. Its absence (which is marked by a hyphen -) means the permission is revoked (not granted).
To see the permissions on a file or directory, use the ls command with long listing option –l
On a file:
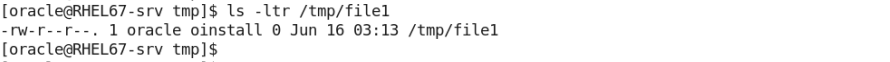
The file is owned by the oracle user and the oinstall group. As oracle user, you can read and write to the file. As any other member of the oinstall group, you can ony read the file. As any other user, you can only read the file.
On a directory:

The home directory of the user ahmed is owned by ahmed and its private group ahmed. Only the user ahmed could list the directory contents of his home directory, create and remove files from it, and change to it. Neither the group nor others have any permissions on that directory.
Summary
- Each file and directory is owned by a user and group.
- Permissions determine what a user or process started by the user could do with a file or directory.
- There are three types of permissions: read, write, and execute.
- There are three categories of permissions: user, group, and others.
- By default, the owner of a file is the user who created the file. The primary group for that user becomes the owner group of the file.
That was part one. See you in part two.



