Although a Vagrant environment, set up in a stand alone mode can satisfy some use cases, such a set up cannot meet all use cases. In a previous tutorial, we discussed how we could use port forwarding to allow easy access to applications using the localhost. This is a use case that is adequately fulfilled in a standalone environment. Using port forwarding does not work well in some situations. These situations are highlighted below.
• The first use case where port forwarding falls short is when we need to identify a machine using its actual hostname. The need to use the actual hostname may arise when SSL certificates are being used or when an application needs the hostname.
• The second use case the port forwarding model is not satisfactory is when we have multiple services set up on a dedicated environment. For example, a web application and the database it uses are set up in different environments.
• A third use case where port forwarding is not appropriate is in a cluster set up where VMs need to be discovered.
After establishing the merit of using networked Vagrant environments, we need to proceed to demonstrate how networking is implemented. Vagrant helps in networking by providing tools for IP address assignment and IP discovery.
The two types of networks that can be set up are local network or bridged network. In a local network, VMs are limited to local host access and the hypervisor is responsible for specifying allowable IP addresses. In a bridged network, there is no constraint on only using IP addresses within the local range. Therefore access to the Vagrant machine happens just like access to any other network host. A bridged network has the disadvantage that Vagrant has no control over IP assignment. The network environment is responsible for IP assignment which poses a difficulty in creating networks.
To begin our demonstration of networking, we will show how to assign an IP address to Vagrant machine. When assigning an IP address to a Vagrant machine it is important to be aware of the private range of IP addresses and ensure any IP address we assign to a Vagrant machine is within the private range. By using only IP addresses that are within the private range, we eliminate the possibility of network conflicts between internal and external environment. In the event of a network conflict arising, the hypervisor will warn you. The Internet Assigned Numbers Authority provides a detailed reference on private IP addresses here http://tools.ietf.org/html/rfc1918.
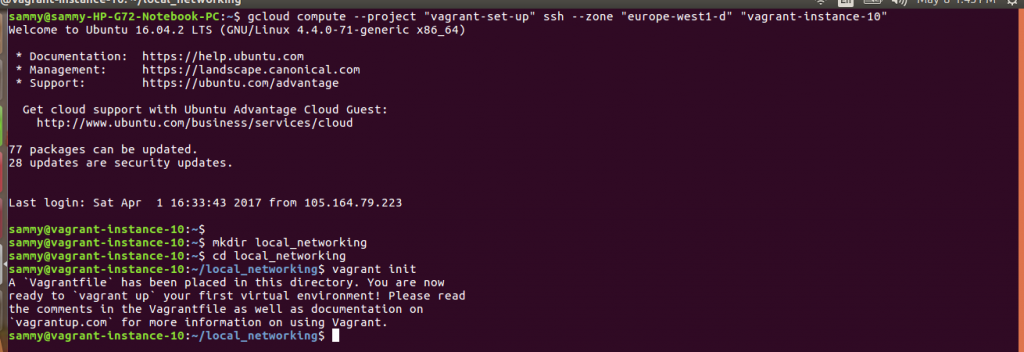
Connect to an instance, create a directory, navigate to the directory and initiate it. The commmands used to accomplish directory set up are shown below:
gcloud compute --project "vagrant-set-up" ssh --zone "europe-west1-d" "vagrant-instance-10" mkdir local_networking cd local_networking vagrant init
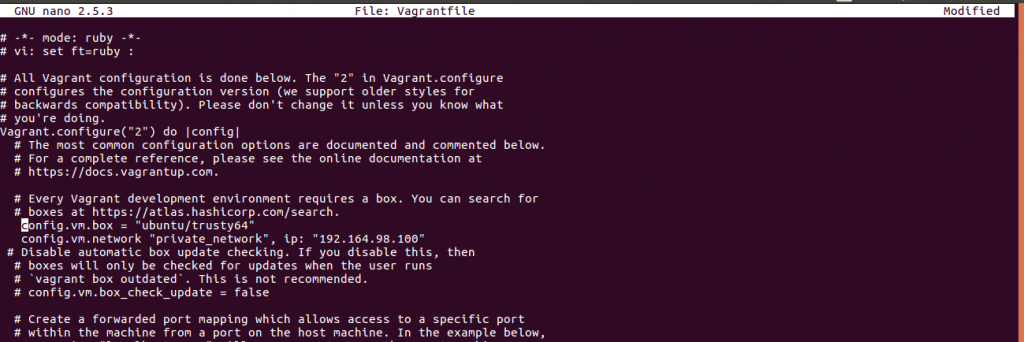
The vagrantfile below shows how an IP address is assigned. In this case, we are using the 192 range. Open the vagrant file created in the previous step and add the contents shown below.
nano Vagrantfile
#specify we would like to use version 2 of the API
Vagrant.configure("2") do |config|
end
#Specify we would like to use Trusty Ubuntu
config.vm.box = "ubuntu/trusty64"
#assign an IP adress to the vagrant machine. Ensure IP is within private range
config.vm.network "private_network", ip: "192.168.99.100"
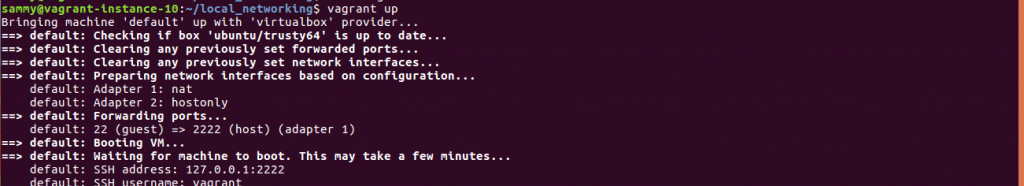
After saving the Vagrantfile, start your machine using the vagrant up command. After the machine is up, access it using vagrant ssh command. We can then use the Vagrant machine terminal to return the range of IP adresses using ifconfig command. Our interest is in the inet addr section, which should reflect the IP adress we assigned to our Vagrant machine. The eth0 interface reflects the IP address that we assigned to our Vagrant machine. The eth1 interface reflects the IP address assigned to the Vagrant machine by the hypervisor. Either IP address can be used to access the Vagrant machine.
In a network, it is preferable to use an actual hostname which is easy to remember instead of the IP address consisting of numbers. This assignment of addresses happens through a Domain Name System(DNS) which holds a register containing addresses and hostnames. When developing locally, we can avoid using a DNS and instead use local hosts file. On Windows or Linux, we just need to add an entry containing our address and host name to the local hosts file.
Apart from editing the local hosts file, there are other approaches we can use to map an address and a host. There are two types of plugins that can be used. In the first type, we use plugins in managing the local hosts file. Vagrant-hosts is one of the widely used plugins for managing the local hosts file. In the second category, we use plugins that act as a local DNS server. Plugins that act as a DNS server will change the guest and host resolver files.
To install the vagrant-hosts plugin, use the command below
vagrant plugin install vagrant-hosts
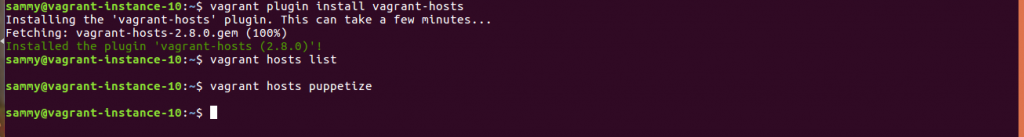
The vagrant-hosts plugin avails two commands at your terminal. The first command vagrant hosts list will return private_network information in a local hosts file format. The vagrant hosts puppetize command will return private_network information in Puppet host format.
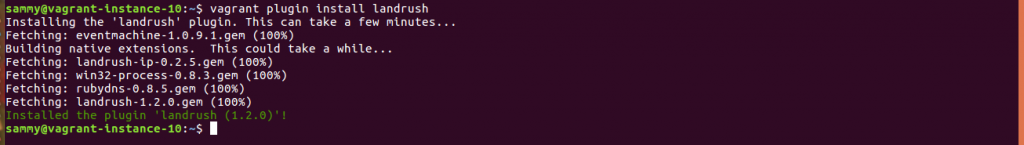
Landrush is one of the widely full featured plugins that can act as a DNS server. To install the landrush plugin, we use the command below.
vagrant plugin install landrush
The landrush plugin is enabled in the Vagrantfile using the entry shown below:
config.landrush.enabled = true
It is important to note when guest machine is shut, any entries that were added will be lost.
To demonstrate how we can configure landrush, an example of mapping a host and an address is shown below. When a host name is not provided it defaults to guest-vm
Vagrant.configure("2") do |config|
config.vm.box = "hashicorp/precise64"
config.landrush.enabled = true
config.vm.hostname = "myhost.vagrant.test"
config.landrush.host 'static1.example.com', '1.2.3.4'
config.landrush.host 'static2.example.com', '2.3.4.5'
end
In this post, we noted port forwarding is use in some cases but there are situations in which it cannot meet our needs. We briefly discussed situations where port forwarding is not appropriate. We introduced local and bridged networks as the two types of networking models that we can use. We demonstrated how we use Vagrantfiles in assigning IP addresses. We also demonstrated how we can use plugins to manage host and address mapping. In this post, we limited our discussion to single machine networks. In part two of networking, we will look at how networking is implemented in a multi-machine environment.




Where is the part 2?