In the previous article, we had a talk on One-Liners. We have seen how a composite statement that is as short as fitting in one line can achieve very useful things that may need a five or ten-lines script to do. In this article, we are going to complete what we have started in the previous one. Enjoy!!
Locating Files of Specific Day (Cont.)
Now, we have this in hand:
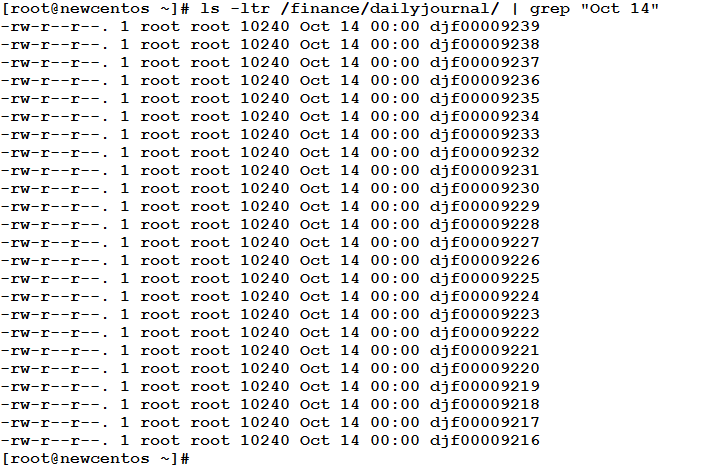
How to extract from this output the filenames and copy them all to another directory (before using scp, winscp, or filezilla to send them via email to the department that asked for them)?!
If you count the fields, you may realize that the filename is the 9th field in the above output. Okay, where are our text-processing tools?!
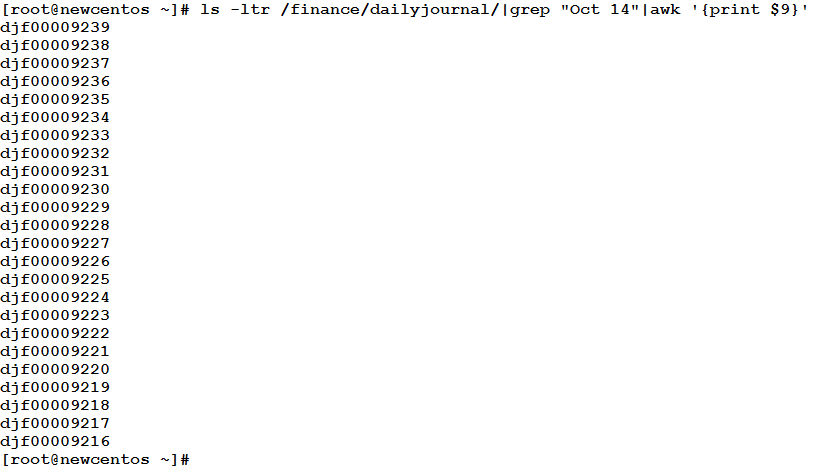
That is it!! Now, we can use a for loop to copy these files one after another to their destination.
Deleting the Defined Disks Problem (AIX)
Based on personal experience, this is a problem that I have faced (which still occurs from time to another). On AIX, for any hardware device to work properly, it must be marked as “Available” in the Object Data Manager (ODM). If for some reason or another, a device is disconnected or powered off, its status becomes “Defined”. In large systems, important data is not stored on local hard disks. It is usually kept on an external storage (SAN) that is connected to the server via fiber cabling. For redundancy and speed, each disk on the storage may be seen from multiple paths (via different fiber cards). Each path appears to the AIX operating system as if it were a child disk for a parent “logical” disk. This parent is what the administrator could use as a physical volume when working with LVM. So, for a large database that requires 4 or 5 terabytes of space, it may need about 100 physical volumes. Now, multiply this by 4 redundancy paths for each physical volume!! Oh!! About 500 (if not more) disks on the system. Now, if for some reason or another, the storage team needs to make a planed outage for some maintenance, or moving the storage from one place to another, they have to power off the storage, and before that, you had to bring down your databases and anything accessing the external storage to avoid unexpected problems.
After powering on things, you will see long list of “Defined” disks. All the disks that were previously available are now marked as defined. If you scan for new hardware, your system will detect the disks again, but will give them numbers after the last used (defined) ones.
Okay, that will not cause a problem, but it is better to remove any defined disks to keep your ODM clean. To remove a device in AIX, the following command is used:
rmdev –Rdl DEVICENAME
But we need to identify the defined disks first:
lsdev –Cc disk|grep –i defined|awk '{print $1}'
This will return the list of defined disks:
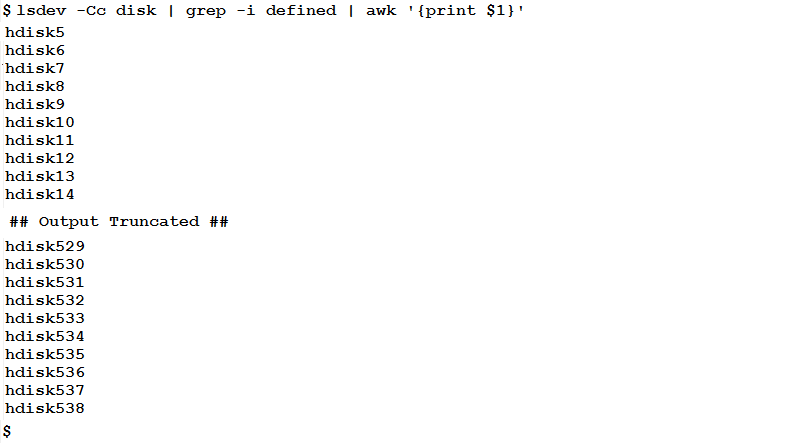
Now, we could delete those disks. To do, we could either use a for loop, or the xargs command:
lsdev –Cc disk| grep –i defined| awk '{print $1}'| xargs –I {} rmdev –Rdl {}
This will delete the defined disks one after another.
Creating User Account and Assigning it a Password
Your manager asked you to create a script that creates a user account, and assigns a random password to it. The script should first check whether there is an existing user with that name on the system. If not, your script should create it and assign it a password. If the user exists, nothing created.
– What do you say?! Do you want to persuade me that all of this could be achieved by one-line code?! Impossible!!
OK, “It always seems impossible until it is done”, as the South African leader Nelson Mandela said.
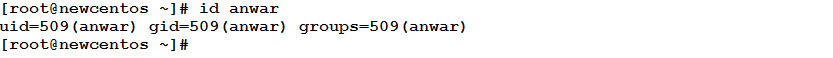
To check if a user exists on the system, there are several ways. My favorite one is using the id command.
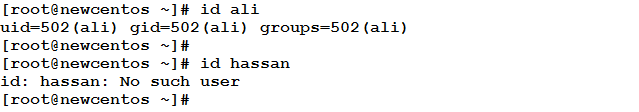
So, the user ali exists, while hassan doesn’t. We need to decide based on the output of the id command whether a user will be created or not. Look at the following statement:
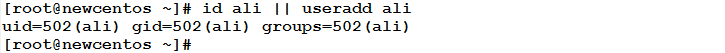
As you remember, the OR operator || will cause the statement on its right side to depend on the first (on the left side). i.e. if the left side statement evaluates to be true (or executed successfully), the right side statement won’t be executed. On the other hand, if the left side statement fails, the right side one will be executed. So, if the command id ali executes without errors (user ali exists), the useradd command won’t be executed (which is the case).
Conversely, consider the case of the user hassan:
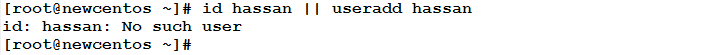
The id command exits with error. So, the useradd command is executed, and the user is created.
Now, it is time to generate a random password and assign it to the new user. I think you also remember the mkpasswd command that creates random passwords. One of the great capabilities of this command is that it could assign the generated password to a user you specify. So, the command now is:
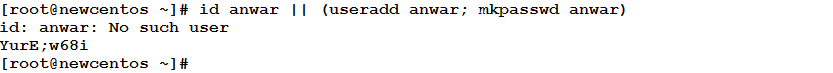
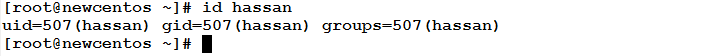
Well, the user has been created and assigned a brand new password. To verify the user is created:
One point left: the silly error message that appears, we should do something to hide it.
![]()
This is if the user already exists. If the user doesn’t exist, the error message that the id command prints won’t be displayed.
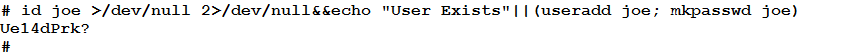
User joe doesn’t exist, so it is created and assigned a new random password, and the password is printed on screen.
All achieved using one line of code!! Isn’t it great?!
* * * * * *
I hope you like this article. See you in the next one.




